Steps for effective cybersecurity incident management
November 29, 2023
Table of contents
Quick Access

Effective cybersecurity incident management is crucial in the ever-changing landscape of digital threats to preserve sensitive information and maintain the integrity of organizational systems.
Data breaches and ransomware attacks are examples of cybersecurity incidents that necessitate a proactive and planned reaction.
In this article, we will look at the important measures for efficient cybersecurity incident management, which will assist organizations in mitigating risks, minimizing damage, and strengthening their overall security posture.
Planning and preparation
Organizations must develop a complete incident response strategy prior to any event. This strategy should create communication methods, clarify roles and duties, and specify the measures to take in the case of a cybersecurity issue. This plan should be updated and tested on a regular basis to verify its relevance and efficacy.
Identifying and Detecting
A cybersecurity event must be identified as soon as possible. To detect odd activity or potential security breaches, use advanced threat detection technologies and monitoring systems. Establish baseline behaviors for regular network and system activity to make detecting anomalies that may indicate an event easier.
Initial Classification and Evaluation
After identifying an occurrence, classify its nature and severity. Consider the influence on the organization's operations, data, and systems. This stage aids in the prioritization of response actions and the efficient allocation of resources.
Eradication and containment
Take action right away to limit the issue and prevent future damage. It may be necessary to isolate impacted systems, close compromised accounts, or block malicious network traffic. To avoid a repetition of the incident, work to eliminate its primary cause.
Analysis and research
Conduct a comprehensive investigation to determine the extent and significance of the occurrence. Analyze the threat actor's tactics, methods, and procedures (TTP). Gather intelligence to bolster future defenses and preserve evidence for possible legal or law enforcement purposes.
Communication and report writing
Throughout the incident response process, maintain clear and transparent communication. If necessary, notify key stakeholders, such as internal teams, senior management, and legal and regulatory organizations. As needed, establish communication channels with external parties such as law enforcement or cybersecurity organizations.
Remediation and Recovery
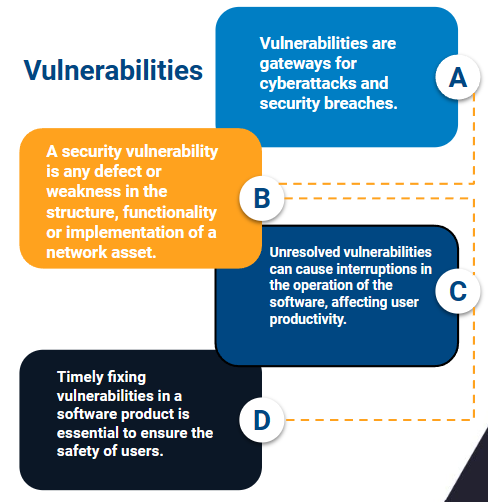
Develop a remediation plan to address vulnerabilities and weaknesses identified during the incident. Make sure all affected systems are completely clean and secured. Implement lessons learned to improve overall cybersecurity measures. Gradually restore normal operations while monitoring for any signs of persistent threats.
Post-incident review
Once the incident is resolved, conduct a post-incident review to evaluate the effectiveness of the response. Identify areas of improvement in the incident response plan, security infrastructure and organizational processes. Use these insights to refine and improve future incident response capabilities.
Training and Awareness
Ongoing training and awareness programs are essential to maintaining a vigilant cybersecurity posture. Educate employees on security best practices, common threats, and how to recognize potential risks. Regularly update training materials to address emerging threats.

It is important to apply correct cybersecurity incident management
Effective cybersecurity incident management is a multifaceted process that requires preparation, vigilance, and adaptability. By following these steps, organizations can respond promptly and efficiently to cybersecurity incidents, minimizing potential damage and improving their resilience to evolving cyber threats.
Regularly review and update incident response plans to stay ahead of emerging threats and ensure the continued security of digital assets.
We recommend you on video
Related Blogs
Free Magento Commerce Features for an Online Store

How to use chatbots for e-commerce?

Which API is best for Android App Development Services
How to automate processes with Odoo software
What programming language is used with React Native?

